Hashing algorithms are essential for securing customer data and ensuring data integrity. Here’s what you need to know:
- Hashing converts data (like passwords or files) into fixed-length, irreversible strings (hashes). It’s a one-way process, unlike encryption.
- Why it matters: Hashing protects sensitive data, prevents breaches, and ensures compliance with regulations like GDPR.
- Key features of secure hashing:
- Pre-image resistance: Prevents reverse-engineering the original data.
- Collision resistance: Ensures no two inputs produce the same hash.
- Deterministic: Same input always produces the same hash.
- Modern algorithms:
- SHA-256/SHA-512: Great for data verification, not for passwords.
- bcrypt, Argon2, scrypt: Best for password security, with features like salting to prevent attacks.
- Hashing vs. Encryption: Hashing is irreversible and ideal for verifying data or storing passwords, while encryption is reversible and used for sensitive data like credit card numbers.
Takeaway: Use modern algorithms like Argon2 for passwords and SHA-256 for data verification. Avoid outdated options like MD5 and SHA-1 to protect data effectively.
Core Features of Secure Hashing Algorithms
Properties That Make Hashing Secure
Secure hashing algorithms are built on a few critical properties that ensure data protection. One of the most important is pre-image resistance – this makes it practically impossible to reverse a hash and uncover the original input. This "one-way" characteristic is what sets hashing apart from encryption. Another key property is collision resistance, which ensures that no two different inputs can produce the same hash. This feature is essential for preventing attackers from swapping legitimate files with malicious ones. Additionally, second pre-image resistance provides extra security by making it infeasible to find a different input that matches the hash of a given input.
Hashing is also deterministic, meaning the same input will always generate the same hash. It produces a fixed-size output, regardless of the input size, which makes it reliable for verifying data integrity. Speed is another important factor – these algorithms must compute hashes efficiently enough to be practical for everyday use.
"A cryptographic hash function must be able to withstand all known types of cryptanalytic attack." – Wikipedia
With these properties in mind, let’s take a closer look at why older algorithms like MD5 and SHA-1 fail to meet modern security standards.
Security Flaws in Older Algorithms
Although secure hashing algorithms are designed to be robust, older ones like MD5 and SHA-1 fall short of today’s security needs. MD5 generates a 128-bit hash, while SHA-1 produces a 160-bit hash. The problem? Collisions can now be computed in mere seconds for MD5, allowing attackers to create two entirely different files with the same hash.
A major blow to SHA-1 came in February 2017 when Google and the CWI Institute in Amsterdam unveiled the "SHAttered" attack. This was the first practical demonstration of a collision for SHA-1. Researchers Marc Stevens and Elie Bursztein managed to produce two distinct PDF files with identical SHA-1 hashes, effectively proving that the algorithm could no longer guarantee collision resistance.
These vulnerabilities underscore why older algorithms are no longer considered secure for protecting sensitive data.
sbb-itb-2ec70df
Current Hashing Algorithms for Marketing Data Protection
SHA-256 and SHA-512 for Data Verification
SHA-256 and SHA-512 are widely used to ensure data integrity as part of your SEO content strategy. These hashing algorithms create unique digital fingerprints for files, databases, and customer records, allowing you to verify that data hasn’t been altered during transfer. By comparing the hash of a file before and after transmission, you can quickly identify any tampering.
Both algorithms are deterministic, meaning the same input will always produce the same hash. SHA-256 generates a 256-bit hash, while SHA-512 produces a 512-bit hash, designed for 64-bit systems. Implementing these protocols is a key component of a robust technical SEO framework. Thanks to their efficiency, SHA-256 hashes can be computed rapidly on high-speed hardware, making them excellent for verifying data integrity. However, these algorithms are not suitable for password storage. Both are FIPS-approved, making them compliant for businesses that handle sensitive marketing data.
"SHA-256 stands as a cornerstone in the world of cryptography algorithms, underpinning the security of digital communications, financial transactions, and data integrity worldwide." – Ethan Carter, Cybersecurity Expert
While SHA-256 and SHA-512 excel at verifying data integrity, they lack the necessary features for securely storing passwords, which require slower and more robust hashing techniques.
Password Hashing with bcrypt, Argon2, and scrypt
When it comes to securing customer passwords, you need hashing algorithms specifically designed to withstand brute-force attacks. Argon2id, the winner of the 2015 Password Hashing Competition, is a standout choice. It provides strong defense against GPU-based and side-channel attacks, earning it the top recommendation from OWASP.
bcrypt is another popular option. It includes an adaptive cost factor, allowing its computational workload to scale with advancing hardware capabilities. However, it does have a 72-byte input limit, which means any characters beyond this limit are ignored. On the other hand, scrypt makes attacks prohibitively expensive by requiring a significant amount of RAM for hash computation, effectively neutralizing hardware like GPUs and ASICs.
Both bcrypt and Argon2 automatically incorporate salting, a process that adds a unique random value to each password before hashing. This feature effectively renders rainbow table attacks useless. These modern hashing methods are essential for safeguarding sensitive password data in today’s digital landscape.
Hashing and Hashing Algorithms – md5 sha1 sha256 sha2 sha3 – Cryptography Essentials
Hashing vs. Encryption vs. Salting: Key Differences
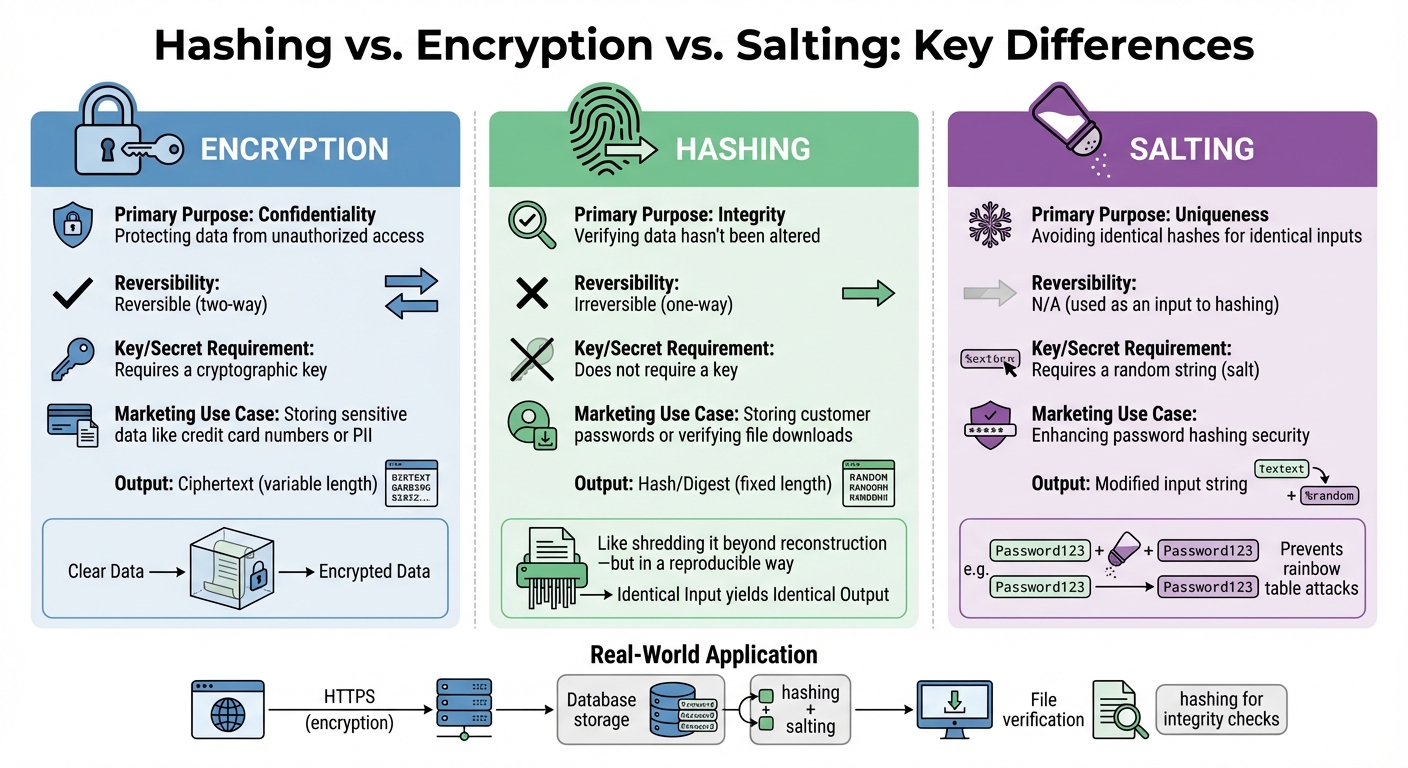
Hashing vs Encryption vs Salting: Key Differences for Data Security
Knowing when to use hashing, encryption, or salting is essential for safeguarding customer data effectively.
Encryption is a two-way process focused on maintaining confidentiality. It transforms plaintext into ciphertext using a key, which authorized parties can use to reverse the process and recover the original data. This method is ideal for storing sensitive information that must remain accessible in its original form, such as credit card numbers, home addresses, or Social Security numbers.
Hashing, by contrast, is a one-way process that generates a unique digital fingerprint, or hash, for your data. Since hashes cannot be reversed to reveal the original input, they are perfect for tasks like verifying data integrity or securely storing passwords. As LoginRadius puts it:
"If encryption is like locking something in a box, hashing is like shredding it beyond reconstruction – but in a reproducible way".
Salting takes hashing a step further by adding a unique, random string to each password before hashing. This ensures that even if two users choose the same password (e.g., "Password123"), their resulting hashes will be entirely different. Salting is particularly effective at preventing rainbow table attacks, which rely on precomputed hash values to crack passwords.
In real-world applications, these methods often work together. Encryption is used to secure data both in transit (e.g., through HTTPS on web forms) and at rest (e.g., in databases storing email lists). Meanwhile, hashing paired with salting protects user credentials, ensuring that even if a database is compromised, attackers cannot retrieve the original passwords.
Each technique plays a distinct role in strengthening data security. Here’s a quick comparison to highlight their differences:
Comparison Table: Hashing, Encryption, and Salting
| Feature | Encryption | Hashing | Salting |
|---|---|---|---|
| Primary Purpose | Confidentiality (protecting data from unauthorized access) | Integrity (verifying data hasn’t been altered) | Uniqueness (avoiding identical hashes for identical inputs) |
| Reversibility | Reversible (two-way) | Irreversible (one-way) | N/A (used as an input to hashing) |
| Key/Secret Requirement | Requires a cryptographic key | Does not require a key (for standard hashing) | Requires a random string (salt) |
| Marketing Use Case | Storing sensitive data like credit card numbers or PII | Storing customer passwords or verifying file downloads | Enhancing password hashing security |
| Output | Ciphertext (variable length) | Hash/Digest (fixed length) | Modified input string |
How Marketers Use Hashing Algorithms
Marketers rely on hashing to protect customer data and maintain the integrity of their information.
Securing Customer Passwords
When users create accounts, hashing transforms passwords into irreversible hashes, adding a layer of security even in the event of a breach. As Dan Arias from Auth0 emphasizes:
"Cleartext storage must never be an option for passwords. Hashing and salting should always be part of a password management strategy".
To strengthen password protection, marketers often combine hashing with salting and peppering. Salts are unique random values added to each password before hashing, while peppers are secret values stored separately. For optimal security, consider using Argon2id with 19 MiB memory and 2 iterations. If that’s unavailable, alternatives like scrypt or PBKDF2 with at least 600,000 iterations can be effective. Avoid outdated algorithms such as MD5 and SHA-1 – researchers estimate that breaking SHA-1 signatures could cost as little as $45,000 using cloud computing resources.
But hashing isn’t just about password security – it’s also essential for ensuring the accuracy and reliability of marketing data.
Verifying Data Integrity
Hashing provides a way to confirm that your data remains unaltered during transfers or storage. By generating a digital fingerprint of your information, you can ensure that customer lists, campaign files, or analytics reports stay intact. For example, when transferring files from a CRM to an email service provider, generating a SHA-256 hash before and after the transfer helps verify the data hasn’t been tampered with.
This method is widely adopted by major tech companies. Mozilla, for instance, offers SHA-256 checksums for Firefox installers so users can confirm their downloads are authentic. Similarly, Ubuntu provides official hash values for its ISO files, allowing users to compare computed hashes with trusted values.
The avalanche effect – where even the smallest change in data results in a completely different hash – makes this approach highly effective for detecting unauthorized modifications. Using algorithms like SHA-256 or SHA-512 for integrity checks, and storing hash values separately from the original data, enhances security and ensures compliance with privacy regulations.
Together, these applications – securing passwords and verifying data integrity – form the backbone of a robust marketing data protection strategy.
How to Implement Hashing Algorithms Correctly
Ensuring secure hashing practices requires not just understanding the theory but also implementing these techniques effectively. For marketers collaborating with development teams, it’s important to grasp the steps that elevate security from basic to robust.
Adding Salts and Peppers to Hashes
Salting involves adding a unique, randomly generated string to each password before hashing. This ensures that even identical passwords produce different hashes. Modern algorithms like Argon2id, bcrypt, and PBKDF2 take care of salting automatically, minimizing the chances of mistakes during implementation.
Salts are particularly effective against rainbow table attacks by introducing a vast range of possible values – 2^128, to be exact. However, poorly implemented salting has been at the root of many security breaches.
Peppering, on the other hand, adds an extra layer of security by incorporating a secret value. This value is stored separately – such as in an HSM, a secrets vault, or a secure variable – and acts as a hidden safeguard. While salts are visible and offer public protection, peppers remain hidden and provide an additional layer of defense.
Another critical step is setting the work factor, which determines how many iterations the algorithm performs. For instance, a bcrypt cost factor of 12 results in each hash taking around 200–300 milliseconds on a modern server. This duration is negligible for users but significantly slows down automated brute-force attacks. The trick is to strike a balance: the hashing process should be long enough to deter attackers but quick enough to avoid slowing down the user experience or triggering Denial of Service (DoS) issues.
With proper salting, peppering, and work factor adjustments in place, it’s essential to address outdated algorithms.
Replacing Outdated Algorithms
Upgrading legacy algorithms is a crucial step in maintaining strong security. Algorithms like MD5 and SHA-1 should be replaced immediately, as they are no longer secure. A notable example is the 2012 Flame spyware incident, where MD5 hash collisions were used to forge counterfeit Microsoft update certificates, allowing malware to masquerade as legitimate updates. This event accelerated the deprecation of MD5 and similar algorithms.
One effective way to transition from outdated algorithms is re-hashing on login. When a user logs in successfully, their password can be re-hashed using modern algorithms like Argon2id (configured with 19 MiB of memory and 2 iterations) or bcrypt (with at least a work factor of 10). For immediate protection of legacy data – before users log in again – you can temporarily wrap the old hash inside a new one, such as bcrypt(md5($password)). However, this method should only be a short-term fix.
"Writing custom cryptographic code such as a hashing algorithm is really hard and should never be done outside of an academic exercise".
To ensure secure implementation, rely on well-established, peer-reviewed libraries like Python’s hashlib or bcrypt. Additionally, implement rate limiting on login attempts to prevent automated scripts from testing thousands of passwords per second.
Conclusion: Using Hashing Algorithms to Secure Marketing Data
Hashing algorithms play a vital role in safeguarding customer data by converting sensitive information into unreadable, fixed-length strings that cannot be reversed. This means that even if a database is breached, attackers would only gain access to meaningless hash values, not the original passwords or personal details. This one-way encryption is why secure hashing is a must-have for marketers.
But hashing isn’t just about protecting passwords. It also acts as a digital fingerprint to ensure data integrity. For example, when transferring customer data sets or marketing files, you can compare hash values before and after transmission to confirm the data hasn’t been tampered with. This step is crucial for maintaining accurate records and complying with regulatory standards.
With data breaches posing ongoing threats to businesses and customers alike, adopting modern hashing algorithms like Argon2id for password storage and SHA-256 for verifying data integrity shows a strong commitment to privacy. When customers see that you’re using trusted, industry-standard security measures, they’re more likely to feel confident sharing their information.
To strengthen your security practices, make Argon2id your go-to for password storage, steer clear of outdated algorithms like MD5 and SHA-1, and always use salting. For organizations needing Federal Information Processing Standards compliance, PBKDF2 with at least 600,000 iterations meets FIPS-140 requirements. Finally, regular security audits ensure your hashing techniques stay effective against advancing threats and hardware capabilities.
FAQs
Why is hashing better than encryption for storing passwords?
Hashing is a one-way process that converts data into a fixed-length string, offering a secure way to store passwords. What makes hashing so effective is that it’s irreversible – there’s no way to reconstruct the original password from the hash. This means that even if someone manages to steal hashed passwords, they can’t turn them back into plain text.
Unlike encryption, hashing doesn’t rely on key management. This eliminates the added complexity and the potential risks associated with decryption attacks. As a result, hashing stands out as a safer and more practical method for safeguarding sensitive user information.
What is salting, and how does it improve password security?
Salting involves appending a unique, random string – called a salt – to each password before it’s hashed. This ensures that even if two users choose identical passwords, their resulting hashes will be entirely different.
By introducing this uniqueness, salting defends against pre-computed attacks like rainbow tables, which depend on matching pre-hashed values. It also makes it much more challenging for attackers to reverse-engineer passwords, even if they manage to access the hashed data.
What are the dangers of using outdated hashing algorithms like MD5 or SHA-1?
Using older hashing algorithms like MD5 or SHA-1 can leave your data exposed to serious security threats. These algorithms are particularly prone to collision attacks, where attackers can generate two different inputs that result in the same hash, undermining the integrity of your data. They’re also vulnerable to cryptographic attacks, which make it easier for malicious actors to decode sensitive information.
To safeguard your customers’ data and uphold their trust, switch to more secure hashing algorithms such as SHA-256 or bcrypt. These modern options are built to handle today’s security challenges effectively.

